CMMC 2.0 for MSPs: What You Actually Need to Know (Not What Vendors Want to Sell You)

CMMC 2.0 enforcement is live. Phase 1 started in November 2025. Phase 2, with mandatory third-party assessments, hits November 2026. If you have defense contractor clients, this is already your problem.
Most CMMC content is written by compliance vendors trying to scare you into buying their platform. This isn't that. This is what MSPs actually need to understand, what your clients are going to ask you, and where the revenue opportunity sits.
The 60-Second Version
The Department of Defense got tired of defense contractors pinky-swearing they were secure. CMMC 2.0 adds real verification on top of the NIST SP 800-171 requirements that have technically been mandatory since 2017.
Three levels:
- Level 1: 17 basic practices, annual self-assessment, covers Federal Contract Information (FCI). If your client has any DoD contract, this is the floor.
- Level 2: 110 controls from NIST 800-171, covers Controlled Unclassified Information (CUI). Most defense contractors land here. Self-assessment or third-party audit depending on how sensitive the data is.
- Level 3: 134 controls, government-led assessment. Reserved for the most sensitive programs. You probably don't have clients here yet.
The timeline that matters: Phase 2 starts November 10, 2026. That's when C3PAO third-party assessments become mandatory for contracts involving critical CUI. Level 2 takes 6-18 months to achieve. If your DIB clients haven't started, they're already behind.
Why MSPs Can't Ignore This
Over 220,000 companies in the Defense Industrial Base need some level of CMMC certification. About 80,000 need Level 2. Most of them are small and mid-size businesses with 20-200 employees.
They don't have internal security teams. They don't have compliance departments. They have an MSP.
Here's what's about to happen: your defense contractor clients are going to call you and ask "can you help us with CMMC?" If your answer is "what's CMMC?", they're going to find an MSP who knows.
This isn't a compliance checkbox. It's contract eligibility. Companies that can't demonstrate CMMC compliance lose the ability to bid on DoD work. For many of your clients, that's their entire revenue stream.
What Your Clients Are Going to Ask You
"Do we need this?" If they have any DoD contract or subcontract, yes. If they handle CUI (technical drawings, specifications, engineering data), they need Level 2. If they only handle basic contract information, Level 1 is the floor. Their contracting officer or prime contractor can confirm what level of data they handle.
"How much does this cost?" Real numbers from the field: Level 1 runs $3,000-$20,000 total. Level 2 self-assessment runs $37,000-$49,000. Level 2 with a C3PAO third-party audit runs $105,000-$118,000. Those numbers include gap assessment, remediation, documentation, and the assessment itself.
"How long does it take?" Level 1: 1-3 months if basic IT security is already in place. Level 2: 6-18 months depending on starting posture and how messy their environment is.
"Can we just fake it?" They've been faking it. That's literally why CMMC exists. The old system was self-attestation with no verification. CMMC adds actual audits. And the penalties for misrepresenting your SPRS score now include False Claims Act liability. That's not a fine, that's federal fraud territory.
The MSP Revenue Opportunity
CMMC readiness isn't a one-time project. It's an ongoing managed service. Here's what the engagement looks like:
Gap assessment ($5,000-$20,000): Evaluate their current controls against NIST 800-171, calculate their SPRS score, produce a remediation roadmap. This is your entry point.
Remediation ($20,000-$80,000+): Implement the technical controls they're missing. MFA everywhere, endpoint detection, SIEM deployment, network segmentation, encryption for CUI at rest and in transit, audit logging, vulnerability scanning. Most of this is stuff you should already be doing for them.
Documentation ($10,000-$25,000): System Security Plan, policies for all 14 domains, incident response plan, POA&Ms for gaps. This is where most organizations fail their assessments. The tech is the easy part. Proving you did the tech is the hard part.
Ongoing monitoring (recurring monthly): Continuous compliance monitoring, quarterly vulnerability scans, annual security training, evidence collection, SPRS score maintenance, annual affirmations. This is the recurring revenue play. CMMC isn't pass-and-forget. It's continuous.
Assessment prep: Mock assessments before the real C3PAO audit. Companies that skip this step fail at significantly higher rates.
One defense contractor client on a full CMMC managed service engagement is worth $50,000-$150,000 in the first year and $2,000-$5,000/month in ongoing monitoring. If you have five DIB clients, that's a new practice area generating $250,000+ in year one.
The Five Things Most MSPs Get Wrong
1. Trying to secure the entire network. CMMC only applies to systems that process, store, or transmit CUI. The smart move is defining a CUI enclave, a segmented boundary where controlled data lives, and locking down just that scope. Smaller scope means fewer controls to implement, lower cost, and simpler assessments.
2. Ignoring documentation. C3PAO assessors verify compliance through documentation review and personnel interviews, not just technical testing. You need an SSP, domain policies, procedures, and evidence artifacts for every single control. If it's not documented, it didn't happen.
3. Waiting for the requirement to show up in a contract. By the time your client sees CMMC in an RFP, they don't have time to get compliant. Level 2 takes 6-18 months. The clients who start now win contracts. The ones who wait lose them.
4. Treating CMMC as just a Level 2 problem. Level 1 applies to every DoD contractor with FCI. That's a much larger pool than Level 2. The 17 practices are basic, but they still require a self-assessment and SPRS submission. This is your door opener for the broader conversation.
5. Not understanding POA&Ms. Plans of Action and Milestones let clients achieve conditional certification with some controls still in progress. But the rules are strict: SPRS score must be at least 88 out of 110, certain high-weight controls can't be on a POA&M, and everything must be closed within 180 days or certification is revoked. POA&Ms are a bridge, not a destination.
How This Connects to Your Existing Services
If you're already providing managed security services, you're halfway there. Map what you already deliver to CMMC domains:
- RMM and patch management covers System and Information Integrity (SI) and Configuration Management (CM)
- MFA and identity management covers Identification and Authentication (IA) and Access Control (AC)
- Endpoint detection covers System and Information Integrity (SI)
- Backup and disaster recovery maps to portions of Media Protection (MP) and System and Communications Protection (SC)
- Security awareness training covers Awareness and Training (AT)
The gap for most MSPs is documentation, audit logging depth, incident response formalization, and evidence collection. Those are the pieces to add, not rebuild from scratch.
What to Do This Week
- Identify your DIB clients. Pull a list of every client with DoD contracts or subcontracts. If you don't know, ask them directly.
- Have the conversation. "CMMC Phase 2 enforcement starts in November. Have you started your assessment?" Most haven't.
- Offer a gap assessment. Position it as a fixed-fee engagement. Deliver an SPRS score and a remediation roadmap. This gets you in the door.
- Build your CMMC practice. Package your existing security stack, add documentation and evidence collection services, and price it as a managed compliance offering.
CMMC isn't going away. The DoD has spent five years building this framework and they're not backing down. The MSPs who build this capability now will own the DIB client relationship for the next decade. The ones who wait will watch those clients leave for an MSP who took it seriously.
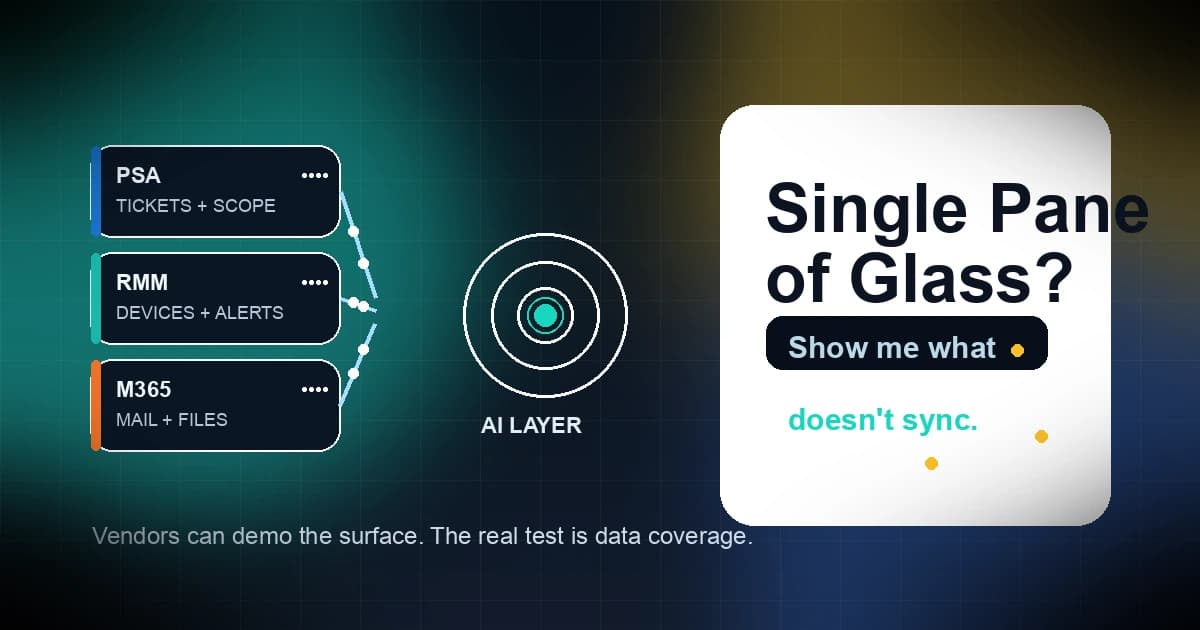
Where Scopable Fits
If CMMC readiness conversations lead to infrastructure quotes (hardware refreshes, security stack deployments, network segmentation projects), those projects need accurate scoping and pricing. Scopable early access gives MSPs a way to pull real client environment data from their PSA and RMM into quotes with margin controls built in, so you're not guessing at the scope of a $50,000 remediation project.
For more on how MSPs are structuring compliance as a revenue stream, see our compliance pricing guide. For the broader compliance liability picture, read our MSP compliance liability guide.